Talks
Offensive AI Agents: How they operate?
| 2026-03-26 | Royal Hacking Lab | US Government & Venture Capital Delegation |
Dr. Emre Süren presented to a delegation of venture capital leaders and representatives from the U.S. Government’s foreign affairs community visiting Sweden, coordinated with the Swedish Embassy in the US. He showcased his current research on offensive-operation agents, comparing modern agentic workflows with manual exploitation techniques from earlier eras. The discussion expanded into practical use cases for personal agents that he uses to manage day-to-day work and life.
Human vs. AI Vulnerability Researcher
| 2026-03-18 | Royal Hacking Lab | Royal Swedish Academy of War Sciences |
Dr. Emre Süren addressed the Royal Swedish Academy of War Sciences. He demonstrated how a security researcher discovers and exploits vulnerabilities in a web application that contained a chain of flaws. For comparison, he presented an AI agent tailored to discover specific web vulnerabilities. The contrast was evident and sparked lively discussion.
Developing Offensive AI Agents
| 2026-03-11 | Royal Hacking Lab | KTH Executive Business School |
Dr. Emre Süren hosted the KTH Executive Business School, led by Ulf Änggård. Dr. Süren showcased hands-on AI agent usage in vulnerability discovery for web applications. Representatives from top 30 companies listed on the Swedish stock market engaged in discussions on how to create AI agents end to end.
An Offensive Security Researcher in AI Era
| 2026-03-04 | KTH Innovation Hub | KTH EECS Career Fair |
Dr. Emre Süren met with KTH students at the KTH EECS Career Fair, sharing insights on being a cybersecurity researcher in AI era. Dr. Süren demonstrated an autonomous hacker agent that exploited a series of vulnerabilities in a website, ultimately granting full system access. He also shed light to the future of the cybersecurity ecosystem, the skills in demand, and essential topics students should master before graduation.
Taking Down Adversarial Infrastructure
Dr. Süren demonstrated his threat intelligence research covering the Cyber Criminal Neutralization Agent to an audience of Swedish military and NATO SACT, which showcased taking down adversarial infrastructure (Sentinel) targeting critical infrastructure in the region. Dr. Süren provided a briefing to Admiral Pierre Vandier regarding how AI can be used as a counter-attack to deter threat actors.
Secure File Transfer in the AI Era – Resilience at Scale
IBM hosted Dr. Emre Süren for a webinar on secure file transfer in the era of artificial intelligence. The main message was straightforward: in a world where AI relies on vast amounts of constantly moving data, secure and resilient file transfer is no longer merely a feature—it has become critical infrastructure. Dr. Süren delved into the increasing significance of data in transit, the dangers posed by outdated protocols, the principles of zero trust, compliance requirements, and the necessity of high-speed, encrypted, and automated data movement for contemporary enterprises.
CORTEX – An LLM-Driven Framework for Enhanced CTI
| 2026-02-04 | KTH Royal Institute of Technology | Digital Futures | Link 1 |
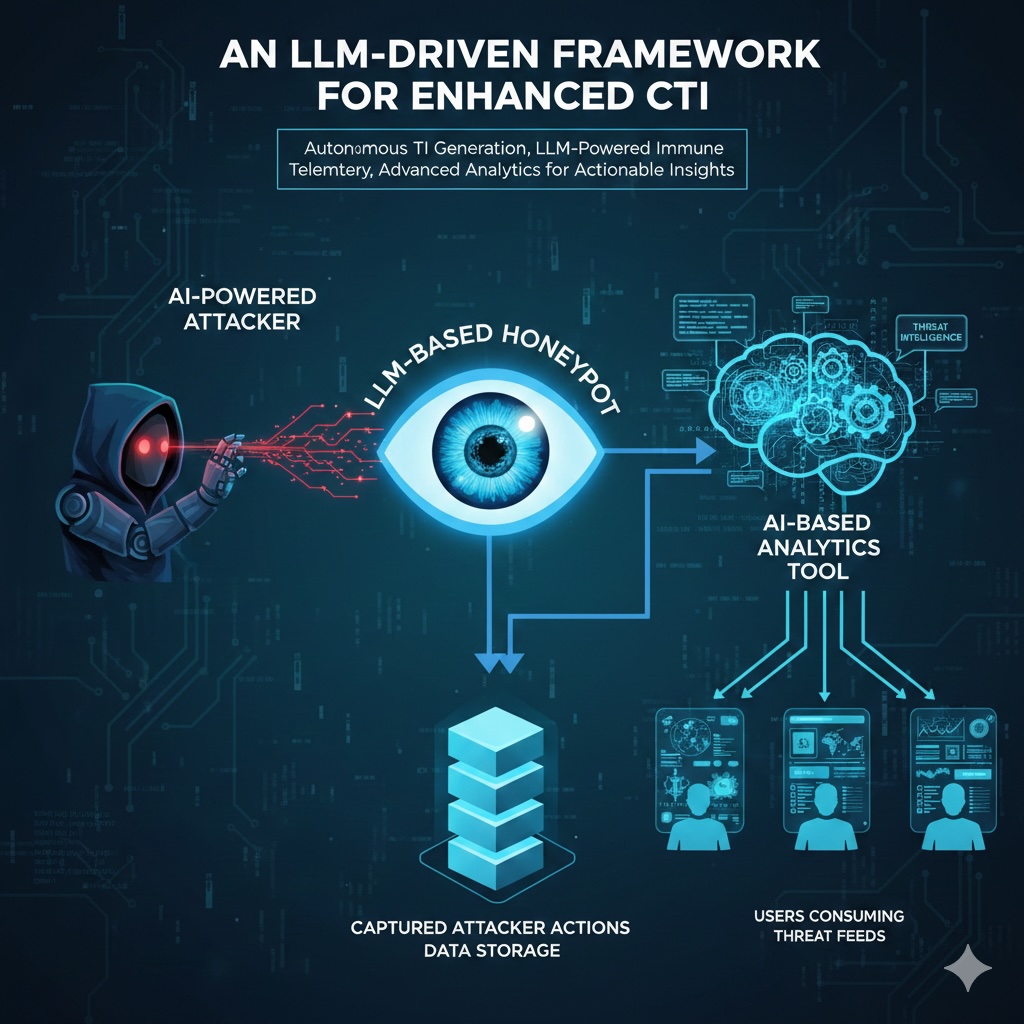 Dr. Emre Süren met with faculty at the Digital Futures event to introduce his latest funded project. He explored how large language models (LLMs) can enhance honeypot development by generating realistic responses and integrating seamlessly into emulated services. The discussion covered techniques for producing authentic answers with LLMs and strategies to prevent internal state leaks.
Dr. Emre Süren met with faculty at the Digital Futures event to introduce his latest funded project. He explored how large language models (LLMs) can enhance honeypot development by generating realistic responses and integrating seamlessly into emulated services. The discussion covered techniques for producing authentic answers with LLMs and strategies to prevent internal state leaks.
Cybersecurity Landscape: Current Trends and Near-Future Outlook
| 2026-01-28 | KTH Nymble | Fusion Career Fair |
 Dr. Emre Süren met with KTH students at the Fusion Career Fair, sharing insights on the future of the cybersecurity ecosystem, the skills in demand, and essential topics students should master before graduation. He recommended platforms for gaining hands-on experience. During his presentation, Dr. Süren demonstrated an AI hacking agent that exploited a chain of vulnerabilities in a website, ultimately granting full system access.
Dr. Emre Süren met with KTH students at the Fusion Career Fair, sharing insights on the future of the cybersecurity ecosystem, the skills in demand, and essential topics students should master before graduation. He recommended platforms for gaining hands-on experience. During his presentation, Dr. Süren demonstrated an AI hacking agent that exploited a chain of vulnerabilities in a website, ultimately granting full system access.
AI for Offensive Security - Autonomous Red Teaming
 Dr. Emre Süren delivered a pitch at the Connect4Cyber matchmaking event organized by the National Coordination Centre (NCC-EE) of Estonia. He also highlighted his contributions to open-source prompt injection tools and ongoing collaborative red teaming activities at his lab. Responding to attendee interest after the presentations, Dr. Süren demonstrated an autonomous hacking agent in action.
Dr. Emre Süren delivered a pitch at the Connect4Cyber matchmaking event organized by the National Coordination Centre (NCC-EE) of Estonia. He also highlighted his contributions to open-source prompt injection tools and ongoing collaborative red teaming activities at his lab. Responding to attendee interest after the presentations, Dr. Süren demonstrated an autonomous hacking agent in action.
Opening Talk of 2026
| 2026-01-14 | Royal Hacking Lab | Swedish Defence University |
 Dr. Emre Süren delivered the opening presentation of 2026 in the Royal Hacking Lab to a group of young interns from the Swedish Defence University who will play a crucial role in defending the nation in the future. The interns engaged in thought-provoking discussions about the hacking agent demonstrated during the practical session.
Dr. Emre Süren delivered the opening presentation of 2026 in the Royal Hacking Lab to a group of young interns from the Swedish Defence University who will play a crucial role in defending the nation in the future. The interns engaged in thought-provoking discussions about the hacking agent demonstrated during the practical session.
LLMs in Offensive Security
| 2025-12-18 | KTH Nymble | Cicor Group | Link 1 |
 Dr. Emre Süren delivered an interactive talk at the Christmas event organized by Cicor Group for its employees. The hands-on workshop demonstrated an autonomous hacking agent, sparking engaging conversations among attendees. Additionally, Dr. Süren introduced his new research grant in Cyber Threat Intelligence and discussed emerging challenges in Sweden’s Internet.
Dr. Emre Süren delivered an interactive talk at the Christmas event organized by Cicor Group for its employees. The hands-on workshop demonstrated an autonomous hacking agent, sparking engaging conversations among attendees. Additionally, Dr. Süren introduced his new research grant in Cyber Threat Intelligence and discussed emerging challenges in Sweden’s Internet.
Digital Forensics Expertise Testimony
| 2025-12-12 | Stockholm | Criminal Court (Tingsrätt) | Link 1) |
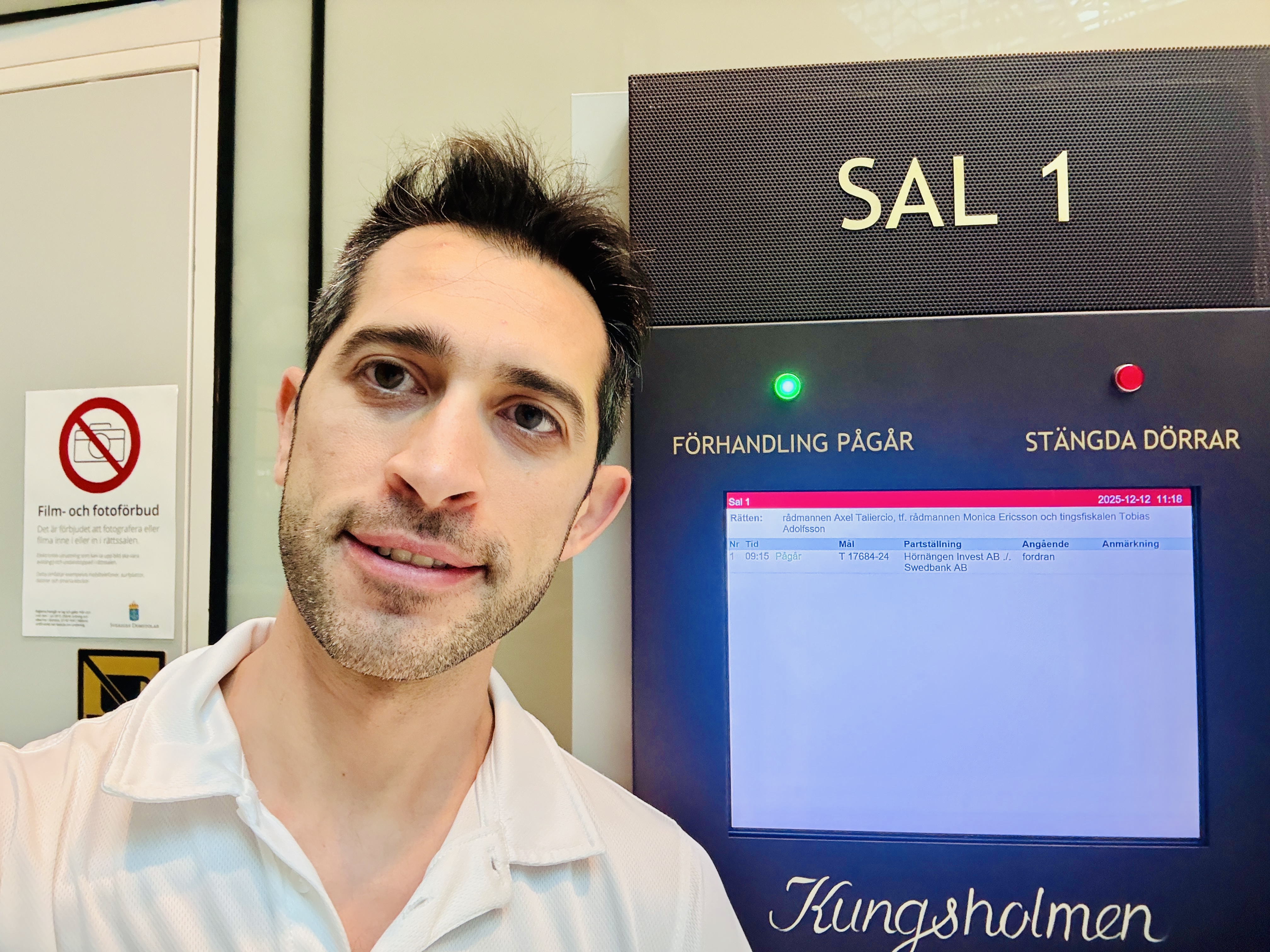 Dr. Emre Süren served as an expert witness for the Stockholm Criminal Court in a high-profile case involving a victim and one of Sweden’s largest banks. Based on forensic analysis of the defendant’s computer, he compiled a detailed report identifying the parties responsible at each stage of the incident. Through his expert testimony, Dr. Süren demonstrated his commitment to public service by contributing his cybersecurity expertise to the justice system.
Dr. Emre Süren served as an expert witness for the Stockholm Criminal Court in a high-profile case involving a victim and one of Sweden’s largest banks. Based on forensic analysis of the defendant’s computer, he compiled a detailed report identifying the parties responsible at each stage of the incident. Through his expert testimony, Dr. Süren demonstrated his commitment to public service by contributing his cybersecurity expertise to the justice system.
Practical Adversarial GenAI for Red Teamers (Workshop)
 Dr. Emre Süren delivered a hands-on workshop at the European Central Bank, demonstrating practical experiments in adversarial GenAI techniques. The session covered prompt injection attacks, jailbreaking methodologies, and the deployment of autonomous penetration testing agents, providing participants with direct experience in offensive AI security research.
Dr. Emre Süren delivered a hands-on workshop at the European Central Bank, demonstrating practical experiments in adversarial GenAI techniques. The session covered prompt injection attacks, jailbreaking methodologies, and the deployment of autonomous penetration testing agents, providing participants with direct experience in offensive AI security research.
Research Vision on Offensive AI Security
| 2025-12-04 | Royal Hacking Lab | Forum for Adjunct Professors and Affiliated Faculty |
 Dr. Emre Süren outlined his research vision to the Forum for Adjunct Professors and Affiliated Faculty, summarizing completed studies, near‑term projects, and collaboration pathways. The session covered vulnerability disclosure practices, engagement with manufacturers, integration of results into master’s education, and how the lab’s work aligns with industry needs and upcoming funding opportunities.
Dr. Emre Süren outlined his research vision to the Forum for Adjunct Professors and Affiliated Faculty, summarizing completed studies, near‑term projects, and collaboration pathways. The session covered vulnerability disclosure practices, engagement with manufacturers, integration of results into master’s education, and how the lab’s work aligns with industry needs and upcoming funding opportunities.
AI in Offensive Security: Key Challenges in LLM-Driven Research
 Dr. Emre Süren spoke at SoC’25 Conference, presenting a practical framework for building LLM agents for penetration testing. The talk covered common development challenges and his mitigation strategies, followed by a demo of an autonomous, multi‑step web exploitation scenario.
Dr. Emre Süren spoke at SoC’25 Conference, presenting a practical framework for building LLM agents for penetration testing. The talk covered common development challenges and his mitigation strategies, followed by a demo of an autonomous, multi‑step web exploitation scenario.
Crime Prevention in Hyperspaces
| 2025-11-20 | KTH Royal Institute of Technology | Safeplaces Network & Digital Futures | Link 1 |
 Dr. Emre Süren served as a discussant for Prof. Martin Törngren’s presentation at the seminar organized by Prof. Vania Ceccato. The discussion explored critical security challenges in autonomous transportation, including privacy concerns related to smart vehicles transmitting GPS location data to services outside the EU, and adversarial poisoning attacks that manipulate self-driving systems to misinterpret road signs.
Dr. Emre Süren served as a discussant for Prof. Martin Törngren’s presentation at the seminar organized by Prof. Vania Ceccato. The discussion explored critical security challenges in autonomous transportation, including privacy concerns related to smart vehicles transmitting GPS location data to services outside the EU, and adversarial poisoning attacks that manipulate self-driving systems to misinterpret road signs.
Dr. Süren’s Research Vision
| 2025-11-20 | Royal Hacking Lab | MSB (Swedish Civil Contingencies Agency) |
 Dr. Emre Süren presented the lab’s completed research and upcoming studies to an audience of 40 industry professionals at an event organized by MSB (Swedish Civil Contingencies Agency). The interactive session highlighted how the lab discloses vulnerabilities and interesting conversations with manufacturers, contributes to master’s student education, and prepares graduates to meet the evolving needs of the cybersecurity industry.
Dr. Emre Süren presented the lab’s completed research and upcoming studies to an audience of 40 industry professionals at an event organized by MSB (Swedish Civil Contingencies Agency). The interactive session highlighted how the lab discloses vulnerabilities and interesting conversations with manufacturers, contributes to master’s student education, and prepares graduates to meet the evolving needs of the cybersecurity industry.
Most Impactful Discoveries in the Lab
| 2025-11-04 | Royal Hacking Lab | Three Letter Agency | Link 1 |
 A restricted briefing at the Royal Hacking Lab convened agency representatives to discuss adversarial capability development for good. Dr. Emre Süren delivered a real-world demonstration of device exploitation to illustrate existing capabilities that can be leveraged by the agency.
A restricted briefing at the Royal Hacking Lab convened agency representatives to discuss adversarial capability development for good. Dr. Emre Süren delivered a real-world demonstration of device exploitation to illustrate existing capabilities that can be leveraged by the agency.
Interview with Dr. Emre Süren
 In an interview with Framtidens Karriar, Dr. Emre Süren, Head of the Royal Hacking Lab, discussed the most compelling aspects of his work and outlined his view that autonomous AI agents could serve as research assistants by 2029.
In an interview with Framtidens Karriar, Dr. Emre Süren, Head of the Royal Hacking Lab, discussed the most compelling aspects of his work and outlined his view that autonomous AI agents could serve as research assistants by 2029.
When Language Models Go Offensive: Lessons from the Lab
 Dr. Emre Süren, Head of Royal Hacking Lab, presented his recent research on Agentic Penetration Testing at an event organized by Detectify. He discussed how he approaches LLM-driven penetration testing, identified potential challenges and his proposals to address them.
Dr. Emre Süren, Head of Royal Hacking Lab, presented his recent research on Agentic Penetration Testing at an event organized by Detectify. He discussed how he approaches LLM-driven penetration testing, identified potential challenges and his proposals to address them.
Dr. Süren’s Research Journey
 Dr. Emre Süren, Head of Royal Hacking Lab, delivered a lecture to the Executive School on offensive security and artificial intelligence. He showcased impactful lab research, including car hacking demonstrations and prompt injection attacks targeting generative AI models. The session also highlighted the his first research grant, which will fund a new project on cyber threat intelligence to detect early signals of AI-driven attacks against Sweden’s critical infrastructure.
Dr. Emre Süren, Head of Royal Hacking Lab, delivered a lecture to the Executive School on offensive security and artificial intelligence. He showcased impactful lab research, including car hacking demonstrations and prompt injection attacks targeting generative AI models. The session also highlighted the his first research grant, which will fund a new project on cyber threat intelligence to detect early signals of AI-driven attacks against Sweden’s critical infrastructure.
Contribution to the National Security
| 2025-10-08 | Royal Hacking Lab | KTH Board | Link 1 |
Dr. Emre Süren, Head of Royal Hacking Lab, hosted the KTH University Board and presented the lab’s mission, highlighting how its research advances society, national security, the economy, and local industry. He announced the inaugural research grant awarded to him, enabling a new project focused on cyber threat intelligence to detect early signals of cyber attacks targeting Swedish critical infrastructures.
Dr. Süren’s Research Vision
| 2025-10-06 | Royal Hacking Lab | KTH Innovation | Link 1 |
 Dr. Emre Süren, Head of Royal Hacking Lab, hosted the KTH Innovation team and presented the lab’s recent popular research and forward-looking project proposals, highlighting innovative approaches in vulnerability research.
Dr. Emre Süren, Head of Royal Hacking Lab, hosted the KTH Innovation team and presented the lab’s recent popular research and forward-looking project proposals, highlighting innovative approaches in vulnerability research.
Dr. Süren’s Research Vision
| 2025-09-26 | Royal Hacking Lab | American Congressmen Delegation | Link 1 |
 Dr. Emre Süren presented to a delegation of American congressmen who visited Sweden. He showcased his previous research on vehicle hacking and X-ray device security.
Dr. Emre Süren presented to a delegation of American congressmen who visited Sweden. He showcased his previous research on vehicle hacking and X-ray device security.
Dr. Süren’s Research Vision
| 2025-09-24 | Royal Hacking Lab | MSAB | Link 1 |
 Dr. Emre Süren hosted MSAB, the Swedish company behind XRY, one of the world’s most widely used smartphone forensics tools. During the visit, he presented the lab’s recent results, including discoveries of vulnerabilities in widely used mobile applications in Sweden, insights into discriminating patterns in dual-use Windows binary behavior, and planned projects on AI-driven vulnerability discovery.
Dr. Emre Süren hosted MSAB, the Swedish company behind XRY, one of the world’s most widely used smartphone forensics tools. During the visit, he presented the lab’s recent results, including discoveries of vulnerabilities in widely used mobile applications in Sweden, insights into discriminating patterns in dual-use Windows binary behavior, and planned projects on AI-driven vulnerability discovery.
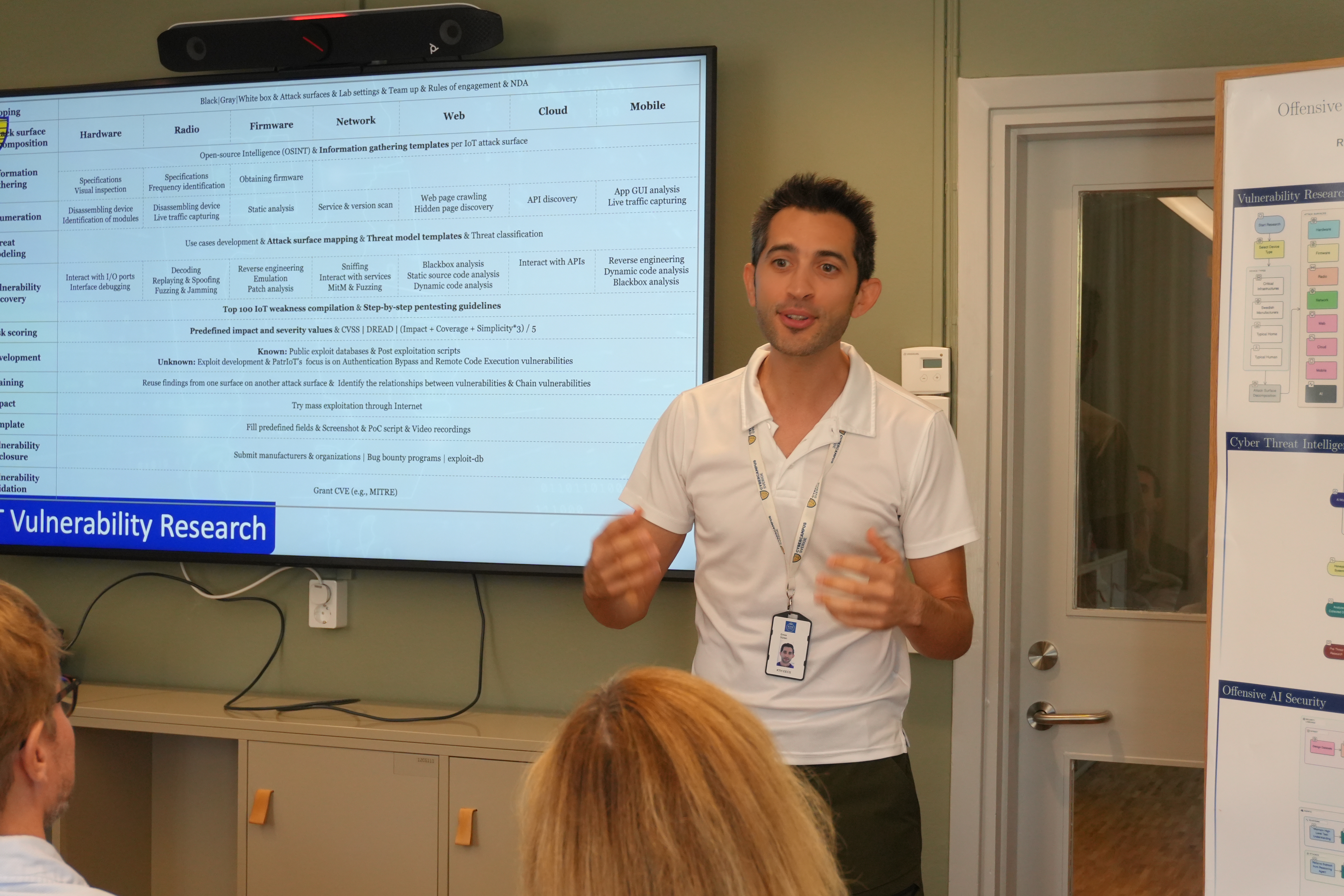
Dr. Süren’s Research Vision
| 2025-09-19 | Royal Hacking Lab | Ministry of Education - Research Policy Unit | Link 1 |
 Dr. Emre Süren, Head of the Royal Hacking Lab, presented the lab’s prior work on IoT security, current research on mobile-application vulnerabilities, and planned projects on AI-driven vulnerability discovery and cyber-threat intelligence. The presentation took place for approximately 20 participants from the Government Offices’ Ministry of Education, Research Policy Unit, and focused on research-policy issues and international research cooperation within the EU.
Dr. Emre Süren, Head of the Royal Hacking Lab, presented the lab’s prior work on IoT security, current research on mobile-application vulnerabilities, and planned projects on AI-driven vulnerability discovery and cyber-threat intelligence. The presentation took place for approximately 20 participants from the Government Offices’ Ministry of Education, Research Policy Unit, and focused on research-policy issues and international research cooperation within the EU.
Proposal: Artificial General Intelligence for Offensive Security
| 2025-06-27 | Online | EU Cybersecurity Funding - Digital EU and Horizon EU 2025 | Link 1 |
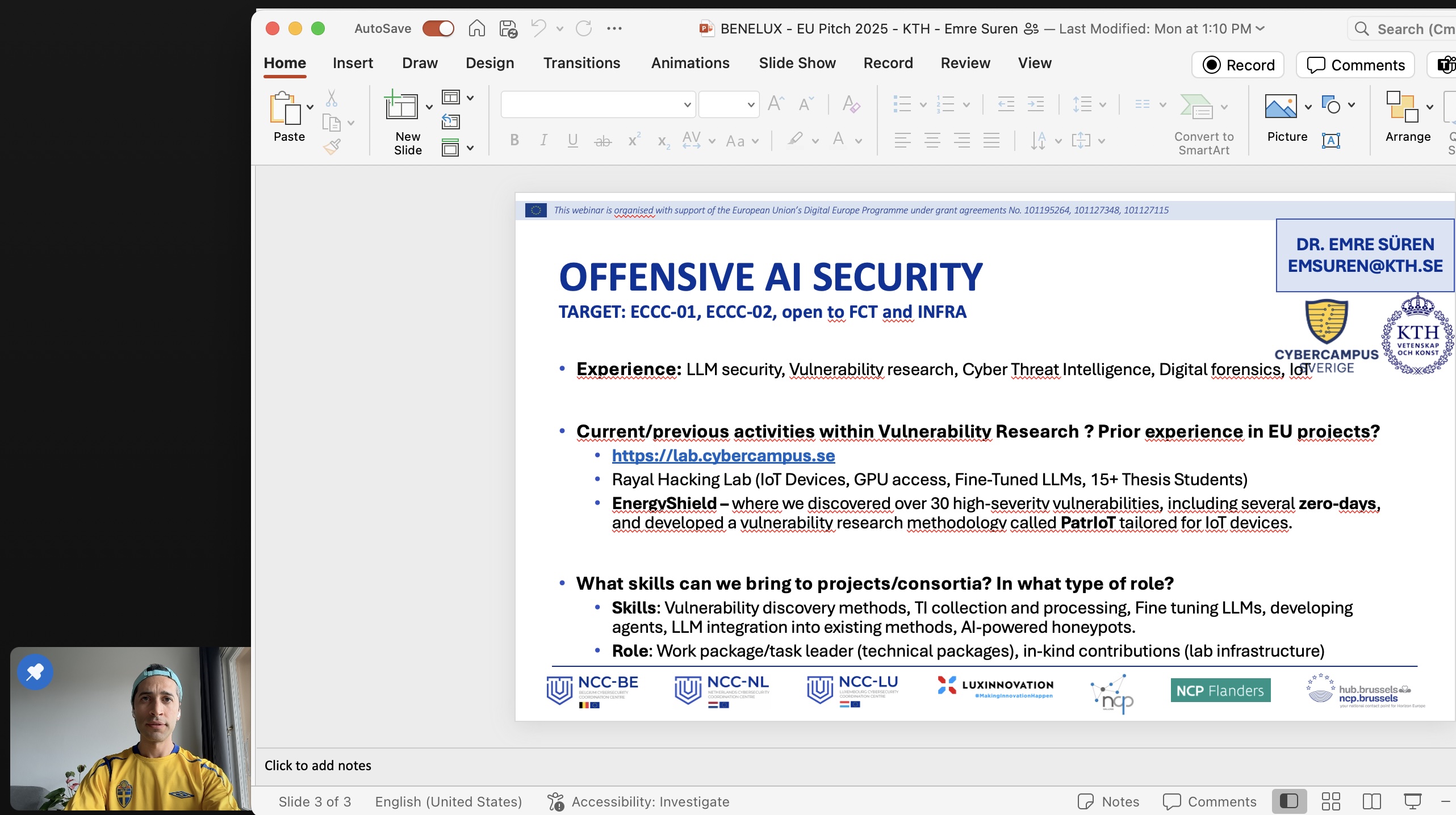 Dr. Emre Süren shared his expertise in vulnerability research, large language models (LLMs) in security, cyber threat intelligence, and digital forensics at the “European Cybersecurity Funding – Digital Europe and Horizon Europe” event, organized by the Benelux NCCs (NCC-NL, NCC-BE, NCC-LU, and the Benelux National Contact Points). The event aimed to identify suitable participants for forming a consortium for the ECCC-01 call.
Dr. Emre Süren shared his expertise in vulnerability research, large language models (LLMs) in security, cyber threat intelligence, and digital forensics at the “European Cybersecurity Funding – Digital Europe and Horizon Europe” event, organized by the Benelux NCCs (NCC-NL, NCC-BE, NCC-LU, and the Benelux National Contact Points). The event aimed to identify suitable participants for forming a consortium for the ECCC-01 call.
Proposal: Offensive AI Security
| 2025-06-12 | Brussels | EU Horizon Cluster 3 Brokerage Event 2025 | Link 1 |
 Dr. Emre Süren, Head of the Royal Hacking Lab, presented a proposal among 25 innovative project ideas to an audience of ~200 participants in Brussels. His proposal focuses on leveraging generative AI for vulnerability research and enhancing Europe’s capabilities to combat crime and terrorism. The aim is to form a strong consortium to apply for upcoming ECCC-X calls.
Dr. Emre Süren, Head of the Royal Hacking Lab, presented a proposal among 25 innovative project ideas to an audience of ~200 participants in Brussels. His proposal focuses on leveraging generative AI for vulnerability research and enhancing Europe’s capabilities to combat crime and terrorism. The aim is to form a strong consortium to apply for upcoming ECCC-X calls.
Dr. Süren’s Research Vision
| 2025-06-03 | Royal Hacking Lab | SWITS’25 Seminar | Link 1 |
 Dr. Emre Süren from the Royal Hacking Lab delivered a live IoT hacking demonstration during the 25th SWITS Seminar, the Swedish IT Security Network for PhD students and researchers. The event brought together around 100 participants who visited the lab in four dynamic sessions, marking the largest, ever visit to the Royal Hacking Lab.
Dr. Emre Süren from the Royal Hacking Lab delivered a live IoT hacking demonstration during the 25th SWITS Seminar, the Swedish IT Security Network for PhD students and researchers. The event brought together around 100 participants who visited the lab in four dynamic sessions, marking the largest, ever visit to the Royal Hacking Lab.
Dr. Süren’s Research Vision
| 2025-05-16 | Royal Hacking Lab | Nanyang Technological University (Singapore) | Link 1 |
 Dr. Emre Süren presented the research done at Royal Hacking Lab to the students from Nanyang Technological University (NTU) Singapore. As NTU is a strategic partner of KTH Royal Institute of Technology, the idea is to draw attention to land exceptional students to the lab.
Dr. Emre Süren presented the research done at Royal Hacking Lab to the students from Nanyang Technological University (NTU) Singapore. As NTU is a strategic partner of KTH Royal Institute of Technology, the idea is to draw attention to land exceptional students to the lab.
Proposal: Offensive AI Security for National Security
| 2025-05-14 | Swedish Defence University | CS4S Matchmaking Event | Link 1 |
 Hacking Lab manager Dr. Emre Süren gave a poster pitch at the Civil Security for Society Matchmaking Event by CrowdHelix to find collaborators for EU Cluster 3 2025 call. Dr. Süren pitched his latest lab work AI-fueled vulnerability research and AI-powered cyber threat intelligence.
Hacking Lab manager Dr. Emre Süren gave a poster pitch at the Civil Security for Society Matchmaking Event by CrowdHelix to find collaborators for EU Cluster 3 2025 call. Dr. Süren pitched his latest lab work AI-fueled vulnerability research and AI-powered cyber threat intelligence.
Dr. Süren’s Research Vision
| 2025-05-08 | Royal Hacking Lab | Nackademin & IT-Högskolan | Link 1 |
 Dr. Emre Süren presented ongoing research in IoT Hacking, Threat Intelligence, and LLM Security to a group of engaged students from Nackademin and IT-Högskolan. The demo contained a series of vulnerabilities (publicly available data, a default password, some weak encoding, and a business logic flaw) causing remote code execution.
Dr. Emre Süren presented ongoing research in IoT Hacking, Threat Intelligence, and LLM Security to a group of engaged students from Nackademin and IT-Högskolan. The demo contained a series of vulnerabilities (publicly available data, a default password, some weak encoding, and a business logic flaw) causing remote code execution.
AI vs. AI: Current Battlefield of Offensive Security
| 2025-04-29 | Royal Hacking Lab | Cybersäkerhetsutbildning för Diplomatprogrammet | Link 1 |
 Dr. Emre Süren, Head of Royal Hacking Lab, delivered a lecture on AI and cybersecurity to Sweden’s next generation of diplomats. As part of their training, diplomatic interns are required to complete a series of cybersecurity modules and he was proud to contribute by offering a session on AI Security within the Cyber Security Training for Diplomats program.
Dr. Emre Süren, Head of Royal Hacking Lab, delivered a lecture on AI and cybersecurity to Sweden’s next generation of diplomats. As part of their training, diplomatic interns are required to complete a series of cybersecurity modules and he was proud to contribute by offering a session on AI Security within the Cyber Security Training for Diplomats program.
Offensive Security in the AI Threat Landscape
 Dr. Emre Süren delivered a guest lecture at Altinget Cybersecurity Network. His presentation focused on key challenges in fine-tuning models for offensive security, optimizing LLM outputs to assist in vulnerability discovery, understanding the limitations of AI agents, and exploring how these models can be utilized in classified environments. He also demonstrated prompt injection attacks on two commercial chatbots.
Dr. Emre Süren delivered a guest lecture at Altinget Cybersecurity Network. His presentation focused on key challenges in fine-tuning models for offensive security, optimizing LLM outputs to assist in vulnerability discovery, understanding the limitations of AI agents, and exploring how these models can be utilized in classified environments. He also demonstrated prompt injection attacks on two commercial chatbots.
Dr. Süren’s Research Vision
| 2025-03-27 | KTH Royal Institute of Technology | KTH Fusion Career Fair - Research Corner | Link 1 |
 Dr. Emre Süren, Head of Hacking Lab, participated in the career fair organized by KTH Fusion (Physics Chapter’s Career Fair 2025), where he had the opportunity to speak with many students about the exciting projects planned in the lab as well as ongoing research.
Dr. Emre Süren, Head of Hacking Lab, participated in the career fair organized by KTH Fusion (Physics Chapter’s Career Fair 2025), where he had the opportunity to speak with many students about the exciting projects planned in the lab as well as ongoing research.
Offensive Security in the AI Revolution
| 2025-03-20 | Detectify | OWASP Meetup | Link 1 |
 Dr. Emre Süren took the stage at an amazing Hack Night organized by OWASP and Detectify. The interactive session dived into: Prompt injection attacks, Fine-tuning LLMs & deploying LLM agents, as well as Current challenges in AI security.
Dr. Emre Süren took the stage at an amazing Hack Night organized by OWASP and Detectify. The interactive session dived into: Prompt injection attacks, Fine-tuning LLMs & deploying LLM agents, as well as Current challenges in AI security.
Offensive AI in Cybersecurity: A Research Outlook
| 2025-03-20 | Royal Hacking Lab | KTH Executive School Guest Lecture | Link 1 |
 Dr. Emre Süren was delighted to host KTH Executive School, with Program Director Ulf Änggård, and valuable staff from Stellar Capacity for an exciting session on cutting-edge cybersecurity research. Dr. Süren presented the current research and future vision, diving into offensive AI, vulnerabilities in the intersection of IoT and LLMs. The session featured: IoT device exploitation – hands-on attack, LLM security weaknesses – practical demonstrations, and a password cracking challenge – a mini-game with the participants.
Dr. Emre Süren was delighted to host KTH Executive School, with Program Director Ulf Änggård, and valuable staff from Stellar Capacity for an exciting session on cutting-edge cybersecurity research. Dr. Süren presented the current research and future vision, diving into offensive AI, vulnerabilities in the intersection of IoT and LLMs. The session featured: IoT device exploitation – hands-on attack, LLM security weaknesses – practical demonstrations, and a password cracking challenge – a mini-game with the participants.
Fundraising for AI research
| 2025-03-03 | KTH Rektorshuset | Hosting a Swedish Philanthropist | Link 1 |
 A restricted event was held at the top floor of KTH Rektorshuset where Dr. Emre Süren presented a demo revolving around vulnerability research and AI.
A restricted event was held at the top floor of KTH Rektorshuset where Dr. Emre Süren presented a demo revolving around vulnerability research and AI.
When AI Hunts AI: Cybersecurity in the Age of Intelligent Threats
| 2025-03-03 | Stellar Capacity | Cybersecurity Masterclass | Link 1 |
 Dr. Emre Süren, Head of Hacking Lab, took the stage at an event organized by Stellar Capacity, where he presented the cutting-edge research he has been leading. His hands-on session demonstrated real-world examples of prompt injection attacks on mainstream LLMs, highlighting the risks these models face in the wild. Beyond showcasing vulnerabilities, he introduced his ongoing work on integrating LLMs into vulnerability research, including fine-tuning models to detect security flaws before they can be exploited.
Dr. Emre Süren, Head of Hacking Lab, took the stage at an event organized by Stellar Capacity, where he presented the cutting-edge research he has been leading. His hands-on session demonstrated real-world examples of prompt injection attacks on mainstream LLMs, highlighting the risks these models face in the wild. Beyond showcasing vulnerabilities, he introduced his ongoing work on integrating LLMs into vulnerability research, including fine-tuning models to detect security flaws before they can be exploited.
Smartwatch Hacking
| 2025-02-20 | Royal Hacking Lab | University of Strathclyde Visit | Link 1 |
 Dr. Emre Süren demonstrated a real-world attack on smartwatches tampering the communication traffic to an audience from a Scottish University.
Dr. Emre Süren demonstrated a real-world attack on smartwatches tampering the communication traffic to an audience from a Scottish University.
Vulnerability Research in the AI Era
| 2024-10-08 | Royal Hacking Lab | Women4Cyber | Link 1 |
 Dr. Emre Süren presented his study in vulnerability research in the AI ecosystem and redesign vulnerability research methods based on LLMs at an event hosted for Women4Cyber. He also provided insights regarding why AI services are considered critical services and the ultimate attack surface.
Dr. Emre Süren presented his study in vulnerability research in the AI ecosystem and redesign vulnerability research methods based on LLMs at an event hosted for Women4Cyber. He also provided insights regarding why AI services are considered critical services and the ultimate attack surface.
Smartwatch Hacking Demonstrated
| 2024-09-27 | Royal Hacking Lab | KTH Rektor and Investment Committee | Link 1 |
 Dr. Emre Süren demonstrated an attack on smartwatches tampering with the communication traffic to the KTH Rector and the rector’s advisory committee for fundraising. The vulnerabilities in this demo were discovered in a lab research.
Dr. Emre Süren demonstrated an attack on smartwatches tampering with the communication traffic to the KTH Rector and the rector’s advisory committee for fundraising. The vulnerabilities in this demo were discovered in a lab research.
Sweden’s Threat Intelligence
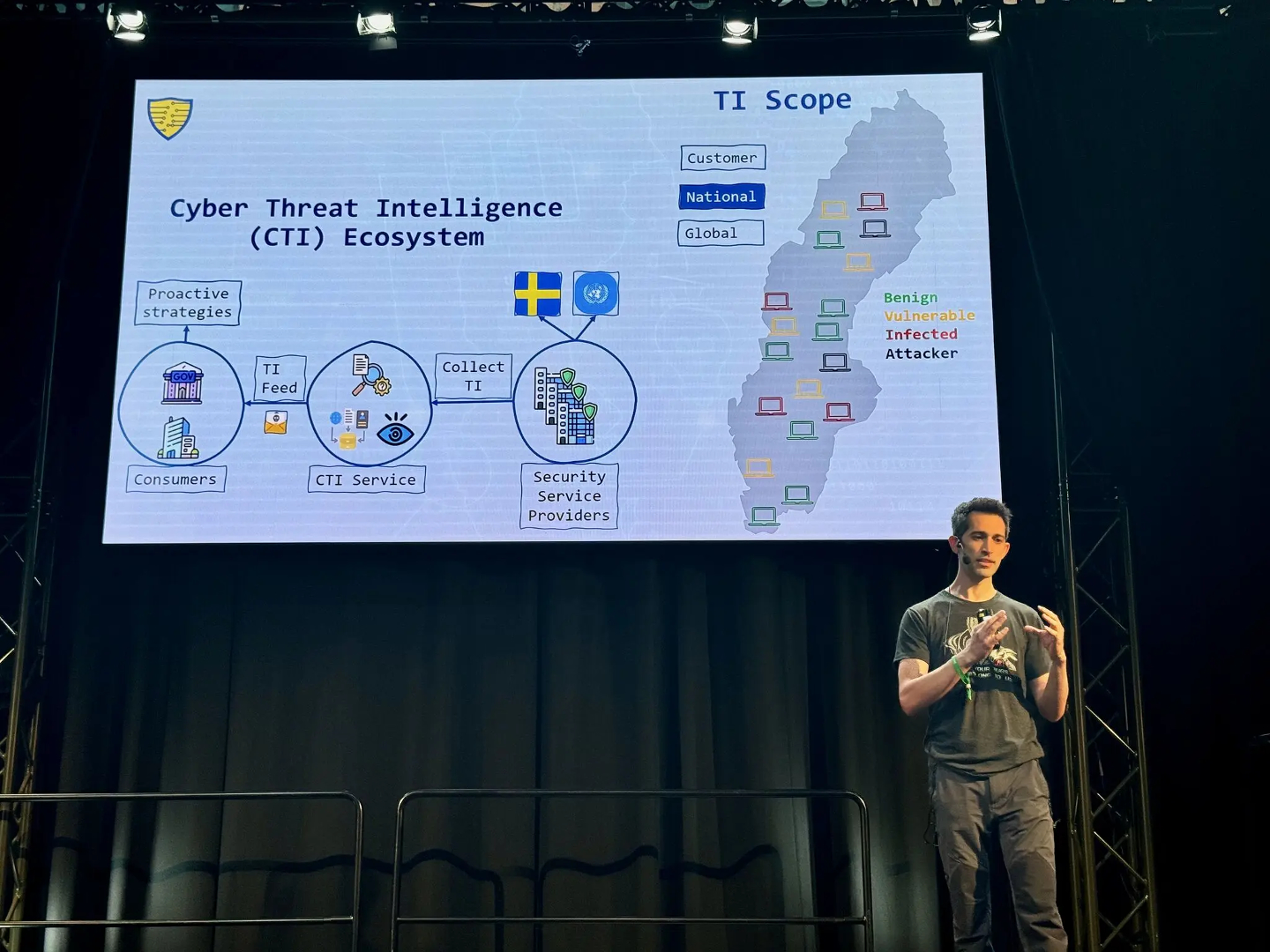 Dr. Emre Süren, Head of Hacking Lab, presented his research, Sweden’s Threat Intelligence, at the Midnight Sun CTF Conference. He showed examples of vulnerable servers and IoT devices, infected devices, and attacker infrastructures all located in Sweden. He proposed an AI-based method to solve the current phenomena.
Dr. Emre Süren, Head of Hacking Lab, presented his research, Sweden’s Threat Intelligence, at the Midnight Sun CTF Conference. He showed examples of vulnerable servers and IoT devices, infected devices, and attacker infrastructures all located in Sweden. He proposed an AI-based method to solve the current phenomena.
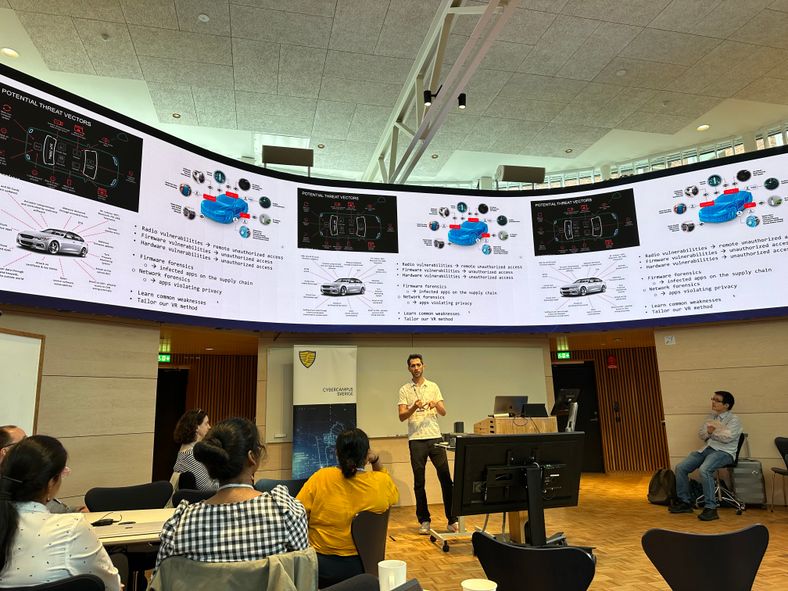
Large Language Models (LLMs) in Security Research
| 2024-06-05 | Royal Hacking Lab | KTH Executive School Visit | Link 1 |
 Dr. Emre Süren is pleased to once again welcome Program Director Ulf Änggård and his participants from the KTH Executive School. Dr. Süren, provided a comprehensive overview of vulnerabilities in cars, charging stations, and smart medical devices. The session also covered the vulnerabilities within the large language model (LLM) ecosystem and explored how LLMs can be utilized for sensitive tasks.
Dr. Emre Süren is pleased to once again welcome Program Director Ulf Änggård and his participants from the KTH Executive School. Dr. Süren, provided a comprehensive overview of vulnerabilities in cars, charging stations, and smart medical devices. The session also covered the vulnerabilities within the large language model (LLM) ecosystem and explored how LLMs can be utilized for sensitive tasks.
Sweden’s Threat Intelligence
| 2024-06-01 | KTH ReaktorHallen | Swedish Stakeholders | Link 1 |
 A classified event was held at KTH Reaktorhallen where Dr. Emre Süren presented the results of his seed project Sweden’s Threat Intelligence.
A classified event was held at KTH Reaktorhallen where Dr. Emre Süren presented the results of his seed project Sweden’s Threat Intelligence.
Hacking Lab Infrastructure and Collaboration Opportunities
| 2024-05-27 | Lund University | SWITS’24 Seminar | Link 1 |
 Dr. Emre Süren was thrilled to be featured at SWITS’24 Seminar, where he had the opportunity to present the lab infrastructure, his ongoing research, and potential collaboration opportunities.
Dr. Emre Süren was thrilled to be featured at SWITS’24 Seminar, where he had the opportunity to present the lab infrastructure, his ongoing research, and potential collaboration opportunities.
Large Language Models (LLMs) in Security Research
| 2024-05-17 | Royal Hacking Lab | KTH Executive School Guest Lecture | Link 1 |
 Dr. Emre Süren was delighted to host participants from the KTH Executive School. Program Director Ulf Änggård, along with the class participants, joined him for an engaging and informative session. Hacking Lab Manager, Dr. Süren, provided an insightful overview of his cutting-edge IoT vulnerability research and demonstrated how he leverage artificial intelligence in his security research. One of the highlights was his renowned smartphone hacking demo, which showcased the practical applications of his research.
Dr. Emre Süren was delighted to host participants from the KTH Executive School. Program Director Ulf Änggård, along with the class participants, joined him for an engaging and informative session. Hacking Lab Manager, Dr. Süren, provided an insightful overview of his cutting-edge IoT vulnerability research and demonstrated how he leverage artificial intelligence in his security research. One of the highlights was his renowned smartphone hacking demo, which showcased the practical applications of his research.
Offensive Security for Medical IoT Devices
| 2024-05-06 | SciLifeLab | HTM Matchmaking 2024 | Link 1 |
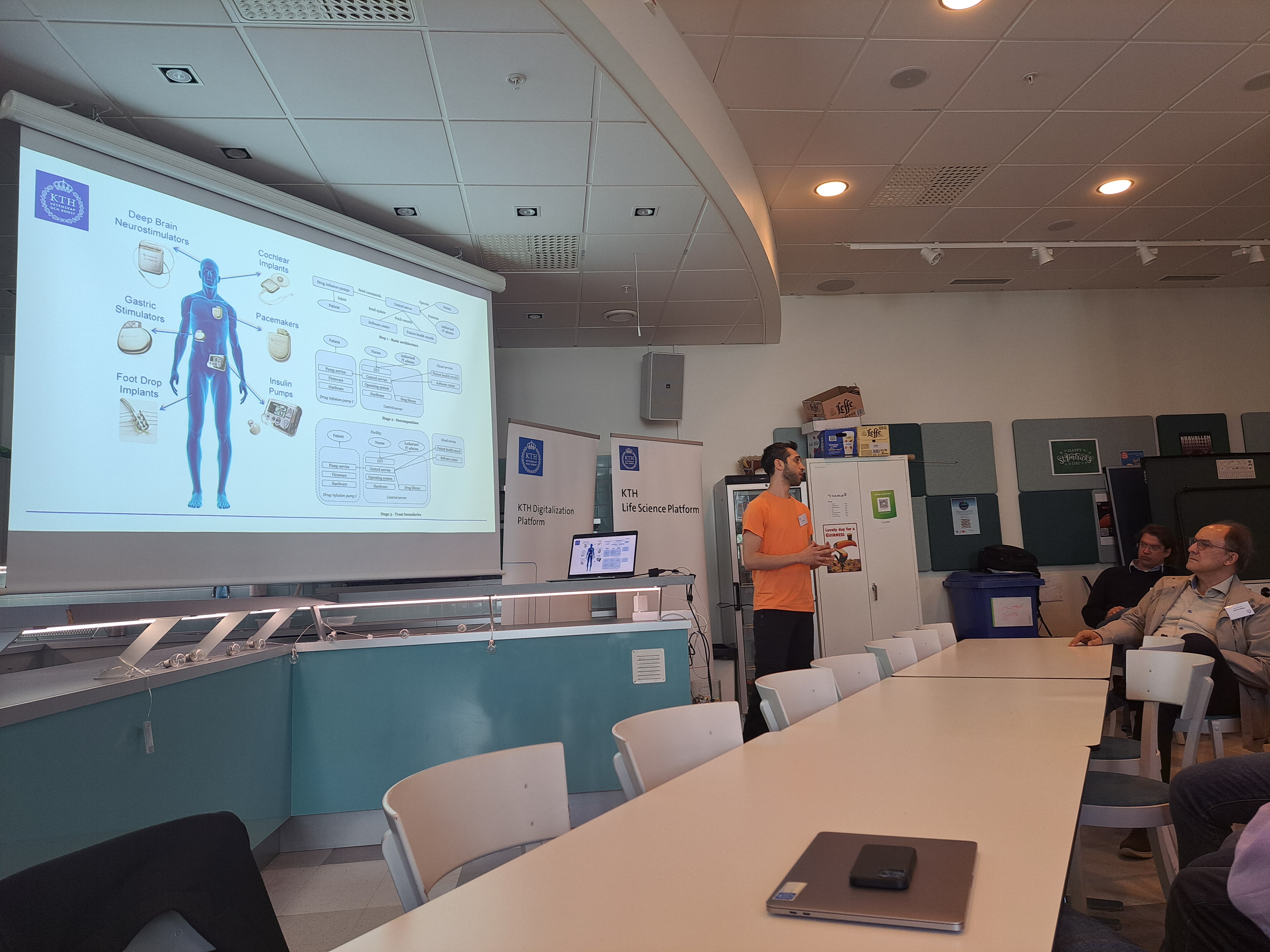 Dr. Emre Süren was excited to share that he had the privilege of presenting at the Health, Medicine, and Technology (HMT 2024) matchmaking event. His pitch shed light on the critical issue of vulnerabilities in today’s medical devices. Dr. Süren demonstrated the importance of leveraging current expertise in IoT vulnerability research to enhance the security of these life-critical devices.
Dr. Emre Süren was excited to share that he had the privilege of presenting at the Health, Medicine, and Technology (HMT 2024) matchmaking event. His pitch shed light on the critical issue of vulnerabilities in today’s medical devices. Dr. Süren demonstrated the importance of leveraging current expertise in IoT vulnerability research to enhance the security of these life-critical devices.
Chat-GPT for Vulnerability Exploitation Demonstrated
| 2024-04-25 | Royal Hacking Lab | Dakota State University Visit | Link 1 |
 Dr. Emre Süren, Head of Royal Hacking Lab, demonstrated an attack involving the use of Chat-GPT for vulnerability exploitation to a delegation consisting of President of Dakota State University Jose-Marie Griffiths, Tommy Schönberg from AI Sweden and Lars Hedström from Försvarshögskolan.
Dr. Emre Süren, Head of Royal Hacking Lab, demonstrated an attack involving the use of Chat-GPT for vulnerability exploitation to a delegation consisting of President of Dakota State University Jose-Marie Griffiths, Tommy Schönberg from AI Sweden and Lars Hedström from Försvarshögskolan.
Beviset: Forum med militära hemligheter utsattes för intrång
| 2024-04-19 | SVT Radio | Interview | Link 1 |
 “Emre Süren, chef på Hacker Lab, en del av Cybercampus på Kungliga Tekniska Högskolan i Stockholm, får se vårt material med rapporten över intrångsförsök på internetforumet med militära hemligheter. Han kan inte utifrån handlingarna dra slutsatsen att någon lyckats hämta ut information därifrån. Men i rapporten finns ett intrång som sticker ut, tycker han. ”Exploited Host”, står det vid ett angrepp som är daterat oktober 2015. Enligt honom betyder det angriparen har kommit in på sajten vid minst ett tillfälle. Det här visar direkt och tydligt att den här enheten har blivit äventyrad av utomstående. En angripare har kommit in på sajten, säger Emre Süren på Hacker Lab.”
“Emre Süren, chef på Hacker Lab, en del av Cybercampus på Kungliga Tekniska Högskolan i Stockholm, får se vårt material med rapporten över intrångsförsök på internetforumet med militära hemligheter. Han kan inte utifrån handlingarna dra slutsatsen att någon lyckats hämta ut information därifrån. Men i rapporten finns ett intrång som sticker ut, tycker han. ”Exploited Host”, står det vid ett angrepp som är daterat oktober 2015. Enligt honom betyder det angriparen har kommit in på sajten vid minst ett tillfälle. Det här visar direkt och tydligt att den här enheten har blivit äventyrad av utomstående. En angripare har kommit in på sajten, säger Emre Süren på Hacker Lab.”
Hacking Lab Showcased for a Government Entity
| 2024-03-25 | Royal Hacking Lab | Interview | Link 1 |
Dr. Emre Süren demonstrated an attack involving the compromise of a fully updated smartphone to the representatives from a government entity. The scenario illustrated the dangers of phishing apps on app stores, which allow attackers direct access to smartphones, the ease of exploiting mobile applications developed without security considerations, the process of guessing passwords that appear to meet secure password policies, the risks of connecting to rogue Wi-Fi networks which expose open services to attackers, and the issue of routers with backdoors enabling attackers to infiltrate networks meant to be secure.
Målet: Nya Cybercampus Sverige ska Stärka Hela Landets IT-säkerhet
 “Studenterna som Ny Teknik träffar har bakgrund från olika ingenjörsutbildningar på KTH, berättar Emre Süren, som forskar om sårbarheter i it-system, med fokus på uppkopplade internet of things-enheter. Han ansvarar också för labbet för etisk hackning på KTH. Vi försöker rekrytera blivande forskare bland våra studenter. Men det är inte vårt enda mål med utbildningen utan vi vill också förbereda studenterna för ett yrkesliv it-säkerhetsbranschen, säger Emre Süren. Nu är tanken att Cybercampus ska bli arenan där akademin och den privata it-säkerhetsbranschen ska kunna mötas under mer formella, strukturerade former. Fördelarna med den typen av utbyte av kunskap och information är stor, enligt forskaren Emre Süren. Vi hoppas kunna fördjupa samarbetet mellan kommersiella it-säkerhetsbolag och forskarvärlden. Inom industrin vill du kanske granska tio spår inom it-säkerhet för att sedan välja ut ett och fördjupa sig i det. Men inom akademin kan vi gå djupare in på fem eller tio intressanta spår parallellt, och sedan jämföra och sortera ut lösningen som är mest intressant. Det är en win-win: Vi skulle kunna ta del av omfattande data som it-säkerhetsbolagen samlar in, och de kan få ta del av vår forskning, fortsätter han.”
“Studenterna som Ny Teknik träffar har bakgrund från olika ingenjörsutbildningar på KTH, berättar Emre Süren, som forskar om sårbarheter i it-system, med fokus på uppkopplade internet of things-enheter. Han ansvarar också för labbet för etisk hackning på KTH. Vi försöker rekrytera blivande forskare bland våra studenter. Men det är inte vårt enda mål med utbildningen utan vi vill också förbereda studenterna för ett yrkesliv it-säkerhetsbranschen, säger Emre Süren. Nu är tanken att Cybercampus ska bli arenan där akademin och den privata it-säkerhetsbranschen ska kunna mötas under mer formella, strukturerade former. Fördelarna med den typen av utbyte av kunskap och information är stor, enligt forskaren Emre Süren. Vi hoppas kunna fördjupa samarbetet mellan kommersiella it-säkerhetsbolag och forskarvärlden. Inom industrin vill du kanske granska tio spår inom it-säkerhet för att sedan välja ut ett och fördjupa sig i det. Men inom akademin kan vi gå djupare in på fem eller tio intressanta spår parallellt, och sedan jämföra och sortera ut lösningen som är mest intressant. Det är en win-win: Vi skulle kunna ta del av omfattande data som it-säkerhetsbolagen samlar in, och de kan få ta del av vår forskning, fortsätter han.”





